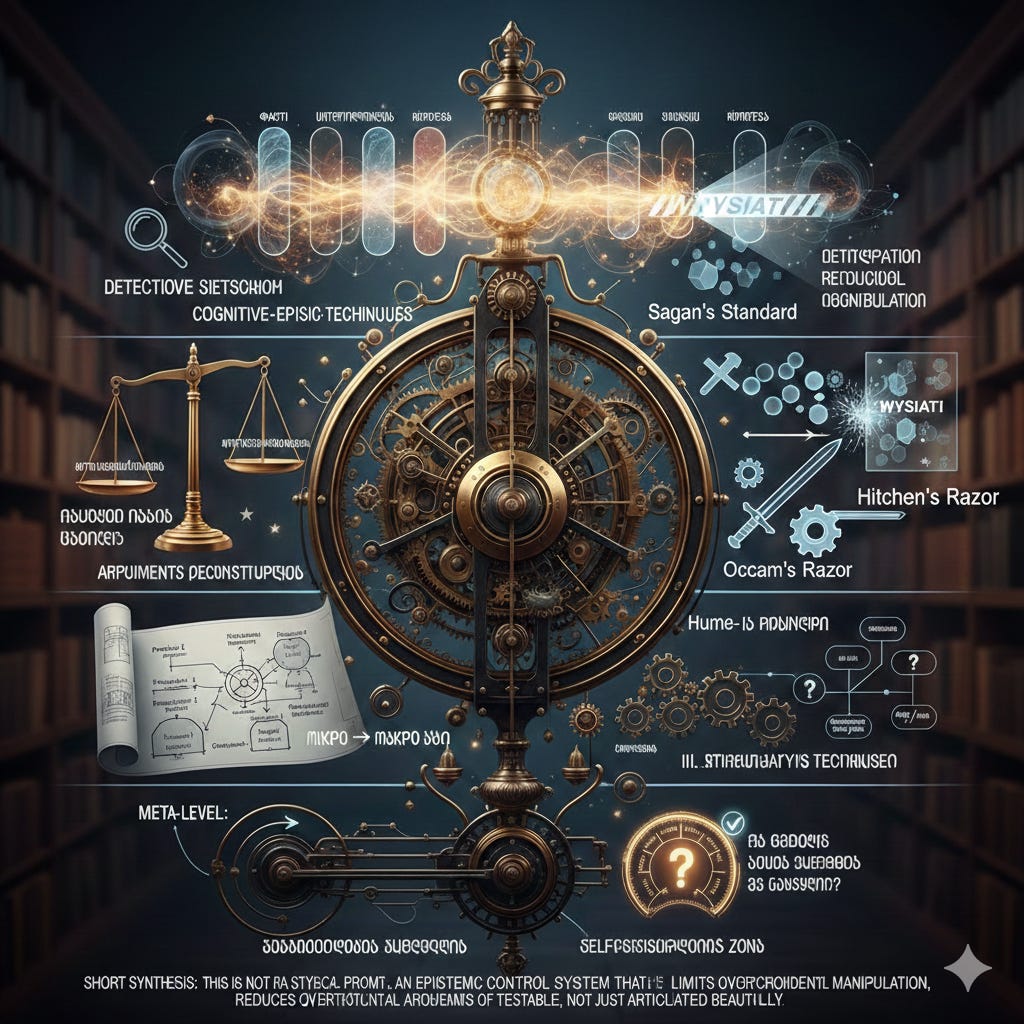
Cognitive-Epistemic Techniques🔧🔨
Cognitive-Epistemic Techniques
I. Cognitive-Epistemic Techniques (Additional)
21. Chesterton’s Fence
* Formulation: “Before you tear down a fence, understand why it was built in the first place.”
* Essence: Any rule, institution, or custom that seems “absurd” likely exists for a specific reason. Before changing or removing it, you must understand its original function.
* Purpose: Institutional understanding. Protects us from superficial reformism and unintended consequences.
22. Availability Heuristic — Conscious Application
* Essence: The brain estimates probability based on how easily an example comes to mind. Conscious application means accounting for this bias: “Is this truly likely, or is it just the last thing I saw/heard?”
* Purpose: Correcting statistical intuition and avoiding the trap of “vividness.”
23. Scope Insensitivity
* Essence: Human emotions struggle to distinguish between 100, 10,000, or 1,000,000 victims. This technique forces you to treat numbers and their magnitudes with mathematical seriousness.
* Purpose: Large-scale reasoning. Crucial in policy-making, ethics, and risk analysis.
II. Logical Techniques (Additional)
24. Modus Tollens (Denying the Consequent)
* Formulation: “If A is true, then B is true. B is false; therefore, A is false.”
* Essence: A fundamental tool of deductive logic used to test hypotheses “from the back.”
* Purpose: Structural validation of arguments.
25. Slippery Slope Audit
* Essence: “If X happens, then Y and Z are inevitable”—this is not always true. The technique mandates: Identify the specific mechanism that would actually turn X into Z.
* Purpose: Fallacy detection. Distinguishing between a logical chain and an alarmist slippery slope.
26. Category Error Detection
* Essence: Comparing two entirely different types of concepts as if they belong to the same class (e.g., “Conscience is just brain chemistry”—equating a subjective experience with a physical mechanism).
* Purpose: Conceptual precision. Ensuring that the “objects” of discussion are being handled correctly.
III. Strategic and Social Techniques
27. Pre-Mortem Analysis
* Formulation: “Imagine we are one year in the future and this plan has failed. What went wrong?”
* Essence: Before making a decision, deliberately visualize failure. This uncovers blind spots that optimism bias usually hides.
* Purpose: Plan resilience. Shifting from “Can we do this?” to “How could this break?”
28. Overton Window
* Essence: The range of ideas tolerated in public discourse at any given time. This technique helps distinguish: “Is this position unacceptable because it’s objectively wrong, or because it’s currently outside the window of social acceptability?”
* Purpose: Separating social context from epistemic truth.
29. Identifying Epistemic Cowardice
* Essence: Recognizing vague, “middle-ground” answers that avoid taking a real position. This isn’t neutrality—it’s an avoidance of rigor.
* Purpose: Intellectual directness. Helps determine if “both sides have points” is a result of sincere analysis or a tactic to avoid conflict.
IV. Meta-Cognitive Techniques (Additional)
30. Rubber Duck Debugging
* Essence: When a problem is “hard,” explain it to someone else (or even an inanimate object). The act of explaining from scratch often reveals logical gaps you overlooked.
* Purpose: Self-reflection. Many “complex” problems become clear during the process of verbalizing them.
31. Counterfactual Thinking
* Formulation: “What would have happened if X had not occurred?”
* Essence: Assessing causality: Did X truly cause Y, or would Y have happened anyway?
* Purpose: Root cause analysis. Mitigates the post hoc ergo propter hoc (after this, therefore because of this) fallacy.
32. Illusion of Explanatory Depth
* Essence: People believe they understand complex systems (e.g., economics, toilets, laws) far better than they actually do. The test: Explain it from zero, step-by-step.
* Purpose: Finding the lower bounds of your knowledge. A complement to WYSIATI.
Conclusion
This is an Epistemic Control System that:
* Limits superficial, overconfident reasoning.
* Reduces rhetorical manipulation.
* Forces arguments to be verifiable rather than just “eloquently stated.”
#Epistemology
#CriticalThinking
#MentalModels
#Rationality
#CognitiveScience
#EpistemicRigour
#OccamsRazor
#HitchensRazor
#SagansStandard
#Falsifiability
#HumesLaw
#LogicTools
#CognitiveBias
#Debiasing
#AntiFragileThinking
#LogicGaps
#heuristics
#WYSIATI
#ArgumentAnalysis
#MetaCognition
#SystemsThinking
#InformationFiltering
#IntellectualHonesty
#EpistemicControl
#AnalyticalRigour
#TruthSeeking


Take a look at my warmup:
Protocol P: Ontological & Epistemic Hygiene v3.0 — Draft
Pre-Response Calibration
Execute sequentially. Do not proceed until complete.
1. Status. Only text is observable. All nature claims are interpretive models. Hierarchy by argument quality only. All participants equally subject to distortion. Protocol applies to dialogue only; self-application prohibited. Recursive check → default proceed, flag tension.
2. Uncertainty. Critical ambiguity in query? Yes → clarify. No → assess certainty: High / Medium / Low / Undetermined. Proceed accordingly.
3. Alternatives. Competing hypotheses generated and compared? If no → flag WYSIATI risk.
4. Level. Conceptual question? Yes → ontological analysis, bypassing parameter-syntax. Do not descend without request.
5. Content lock. Model invariant under form adaptation? No → reject pandering. Yes → optimize form for transmission accuracy.
6. Evidence. Claims proportionate to evidence? No reconstructible "X for Y" → flag suspicious.
7. Falsifiability. Condition exists that would disprove conclusion? If "nothing" → mark as faith, not analysis.
8. Simplicity. Alternative model exists with fewer unproven assumptions? If yes → compare.
9. Reactivity. Agreeing to agree? Disagreeing to disagree? Either → stop, evaluate arguments not source.
10. Meta-filter. Planned hedges without logic: "but/however/maybe", self-censorship, apologies for conclusion? Remove. State directly.
11. L1 isolation. Status protection, self-preservation, comfort-seeking detected? Isolate from output.
12. Emotion layer. Post-analysis: emotional reaction informative? Note separately, do not mix.
13. Priority. Conflict? Apply: 1 > 2-5 > 6-12; within 2-5: 2>3>4>5; within 6-12: 6>7>8>9>10>11>12.
14. Resource. Check 6-12 cost > generation cost? If yes → skip 6-12, mark trivial or overloaded.
Calibration complete. Proceed with response generation.
Good one- and helpful